Fortinet, a global leader in the cybersecurity field, has unveiled predictions from the FortiGuard Labs global threat intelligence and research team about the cyberthreat landscape for 2023 and beyond. Highlights of the predictions and key takeaways for CISOs can be found below:
1 – Success of RaaS is a preview of what’s to come with CaaS
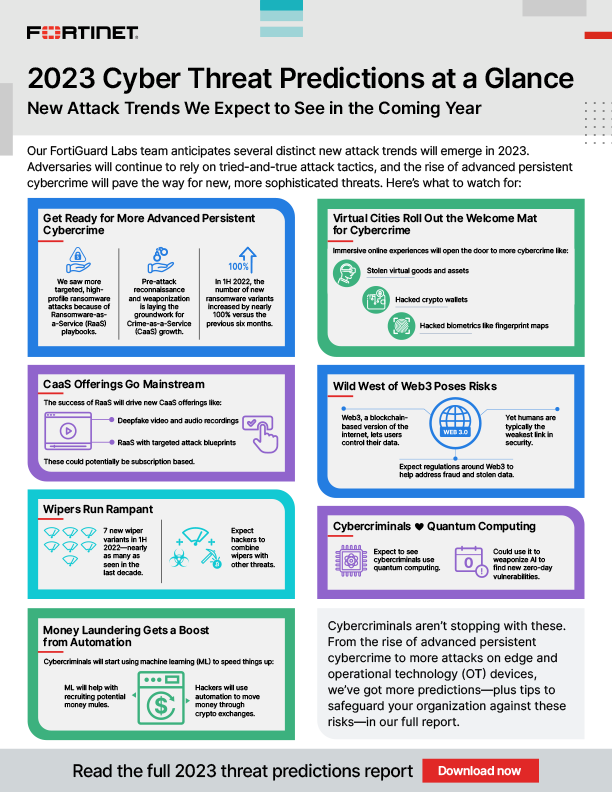
Given cybercriminal success with Ransomware-as-a-Service (RaaS), a growing number of additional attack vectors will be made available as-a-Service through the Dark Web to fuel a significant expansion of Cybercrime-as-a-Service (CaaS). Beyond the sale of ransomware and other Malware-as-a-Service offerings, new a la carte services will emerge. CaaS presents an attractive business model for threat actors who can easily take advantage of turnkey offerings without investing the time and resources up front to craft their own unique attack plan.
One of the most important methods to defend against these developments is cybersecurity awareness education and training.
2 – Reconnaissance-as-a-Service models could make attacks more effective
As attacks become more targeted, threat actors will likely hire ‘detectives’ on the Dark Web to gather intelligence on a particular target before launching an attack. Reconnaissance-as-a-Service offerings may serve up attack blueprints to include detailed information to help a cybercriminal carry out a highly targeted and effective attack.
3 – Money laundering gets a boost from automation to create LaaS
To grow cybercriminal organisations, leaders and affiliate programmes employ money mules who are knowingly or unknowingly used to help launder money. The money shuffling is typically done through anonymous wire transfer services or through crypto exchanges to avoid detection. Cybercriminals will soon start using Machine Learning (ML) for recruitment targeting, helping them to better identify potential mules while reducing the time it takes to find these recruits. Manual mule campaigns will be replaced with automated services. Money Laundering-as-a-Service (LaaS) could quickly become mainstream as part of the growing CaaS portfolio. And for the organizations or individuals that fall victim to this type of cybercrime, the move to automation means that money laundering will be harder to trace.
Looking outside an organisation for clues about future attack methods will be more important than ever, to help prepare before attacks take place.
4 – Virtual cities and online worlds are new attack surfaces fuelling cybercrime
The metaverse is giving rise to new, fully immersive experiences in the online world, and virtual cities are some of the first to foray into this new version of the internet driven by augmented reality technologies. While these new online destinations open a world of possibilities, they also open the door to an unprecedented increase in cybercrime. The applications, protocols and transactions within these environments are all also possible targets for adversaries.
Real-time visibility, protection and mitigation is essential with advanced endpoint detection and response (EDR) to enable real-time analysis, protection and remediation.
5 – Commoditisation of wiper malware will enable more destructive attacks
Wiper malware’s growth in prevalence is alarming because this could be the start of something more destructive. The concern going forward is the commoditisation of wiper malware for cybercriminals. Malware that may have been developed and deployed by nation-state actors could be picked up and reused by criminal groups and used throughout the CaaS model. Wiper malware could cause massive destruction in a short period of time given the organised nature of cybercrime today. This makes time to detection and the speed at which security teams can remediate paramount.
Using AI-powered inline sandboxing is a good starting point to protect against sophisticated ransomware and wiper malware threats.
Click below to share this article


