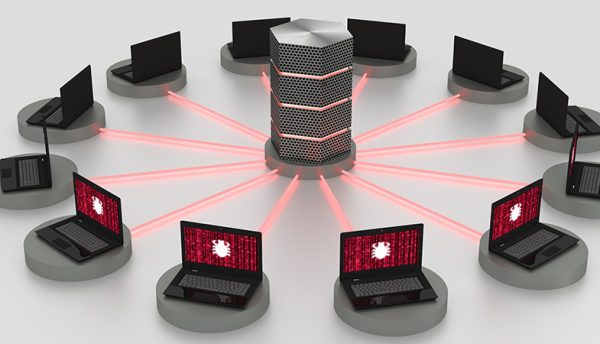
Netskope Threat Labs reveals more than a third of sensitive business...
Generative AI usage more than triples in 12 months but organisations still struggling to balance safe enablement with risk management. Netskope, a leader in Secure Access Service Edge (SASE), has published new...